The Azure Information Protection scanner has been around for some time. It can be used to detect, classify and protect documents which are stored on your fileshares and (on-premises) SharePoint environments.
To know what to scan, the scanner uses data repositories which are stored in the relevant SQL database. Until now, an administrator needed to use PowerShell to manage these repositories. Using cmdlets like Add-AIPScannerRepository new repositories could be added. Or Add-AIPScannerScannedFileTypes is used to add a specific filetype to the list of scanned files.
In my previous posts (Azure Information Protection Scanner, AzureIP news) I mentioned these. But with the new version of the AzureIP client (number 1.48.1.0) this can now be done from the Azure Portal! Hooray! Let’s take a look.
Azure Information Protection portal
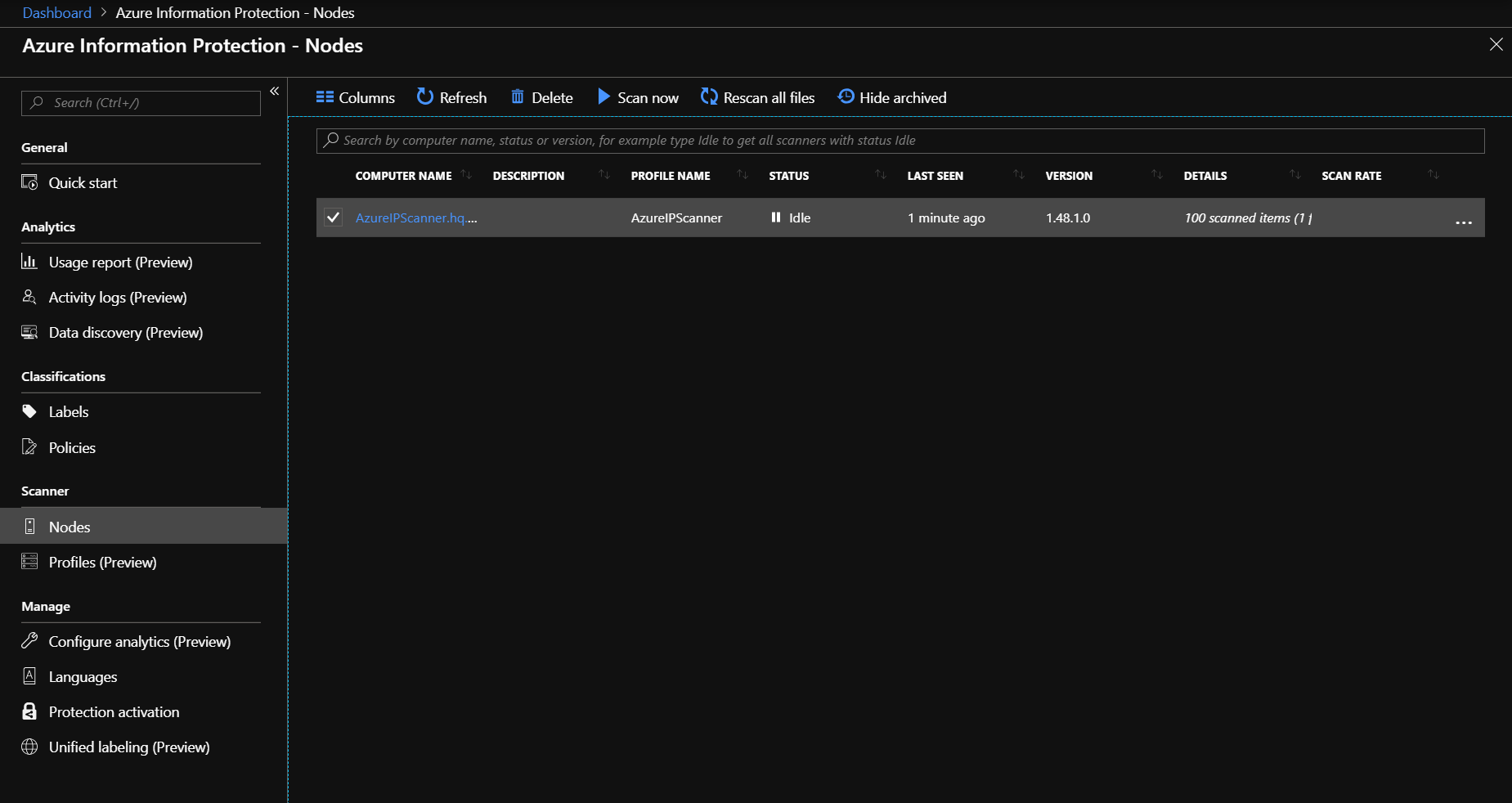
First things first. I like what Microsoft’s doing with the portal. So many preview aspects, logging possibilities and more. One thing I want to mention is the Nodes overview. This gives you an overview of all your scanners and you can even start/stop a scan from this portal.
Profiles
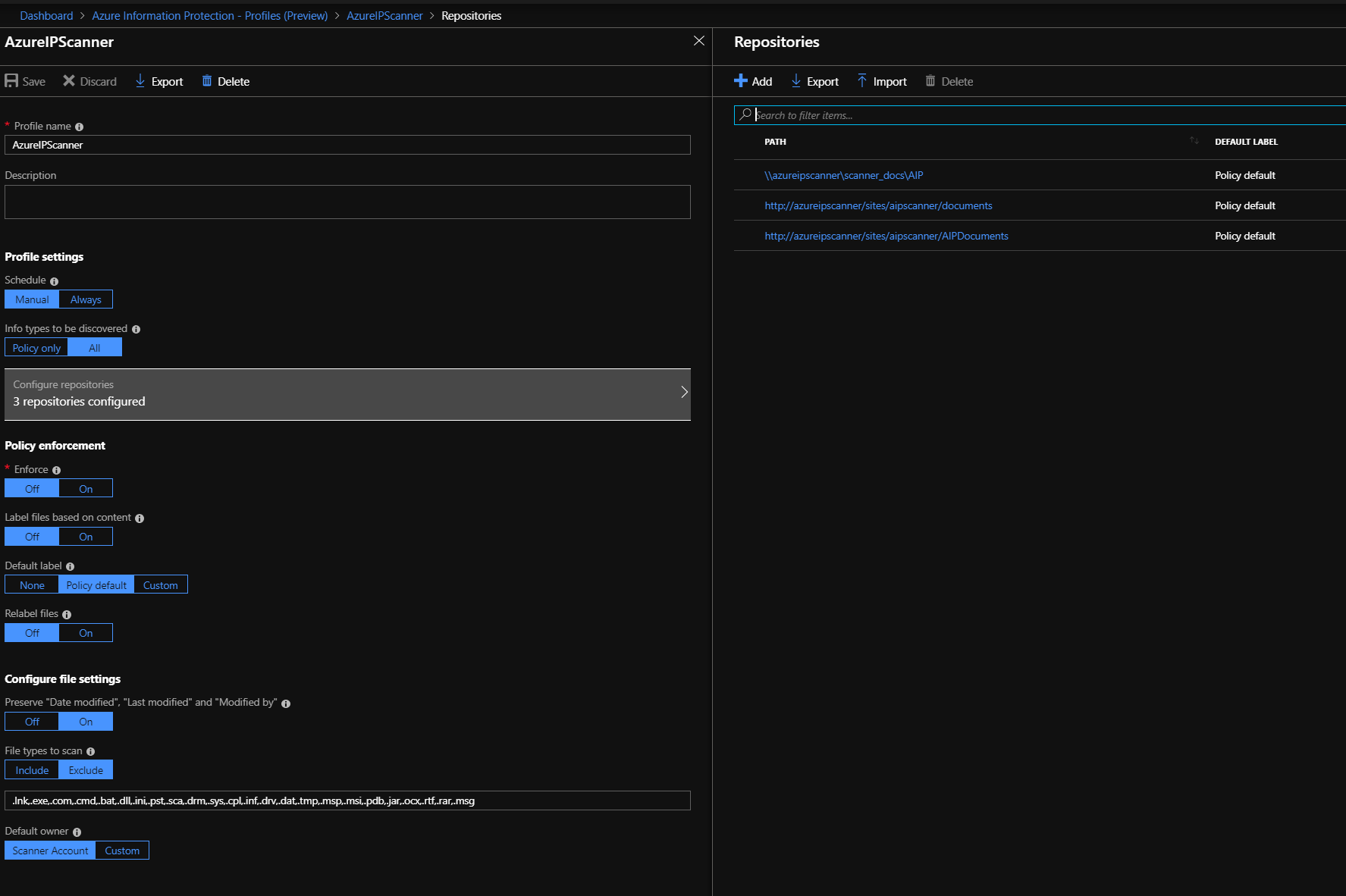
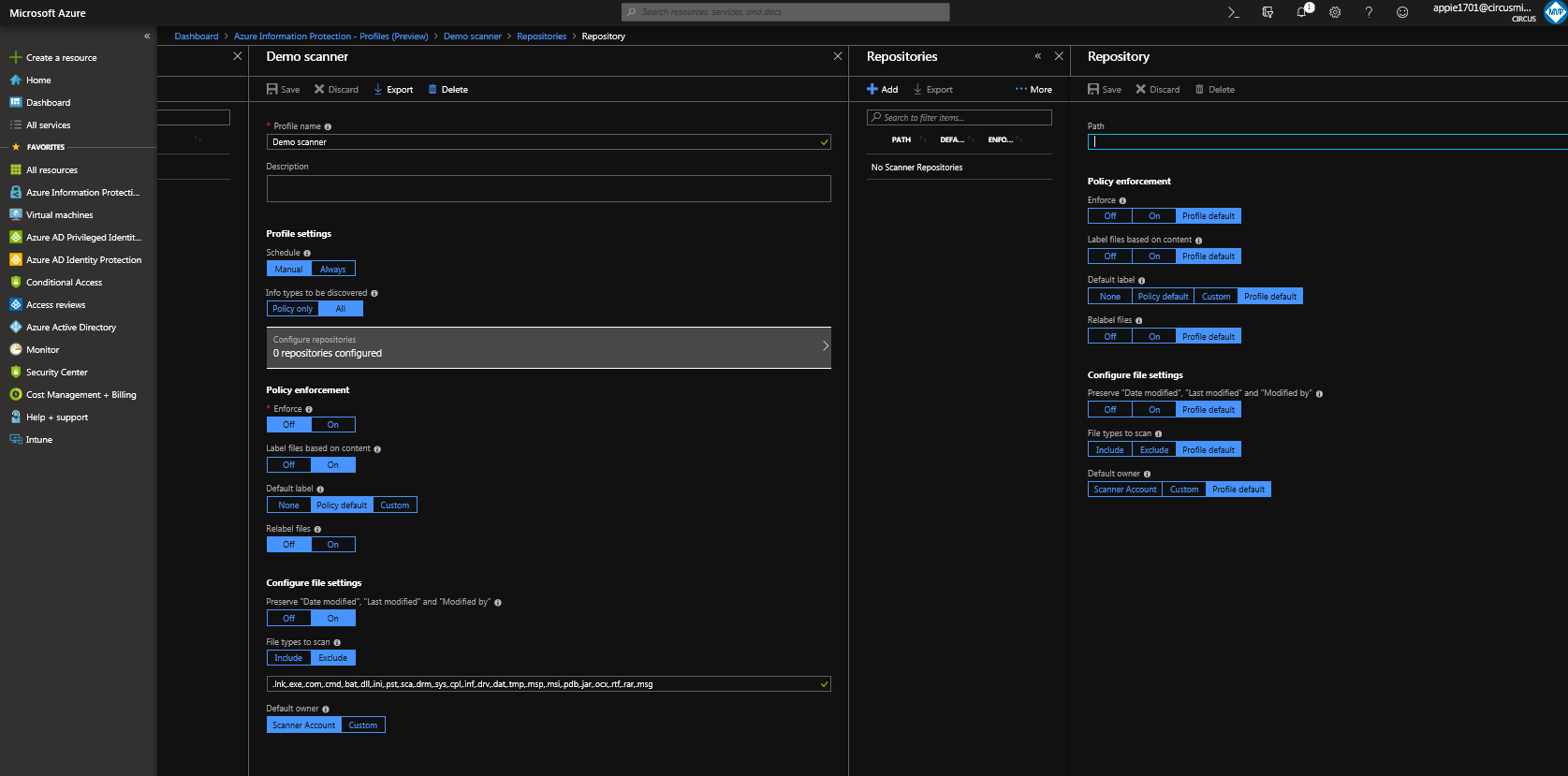
The Profiles section is the place to go for your configuration. Here your can set a policy (which is generic) with one or more repositories. Please note that you can only add repositories after you’ve initially saved the profile. Kinda weird, but it works.
The settings in the profile and repositories contain the same settings as the previous PowerShell cmdlets. Including the relevant settings for preserving relevant metadata (like “Modified by”). So take care with these.
One thing to notice: where do I specify which scanners use this policy?
The answer (for now), you configure that when upgrading the scanner (see below).
Upgrading the scanner
In order to use this new function, you will need to upgrade the Azure Information Protection software on the scanner. First, download the preview-client from the download site. And then, please take note! Do not just install this new version. It does require some little additional steps.
- Stop the Azure Information Protection Scanner service;
- Install the new client;
- Using PowerShell, run the Update-AIPScanner -profile <profile> cmdlet;
- Start the Azure Information Protection Scanner service.
In step 3 you use the profile you created earlier. 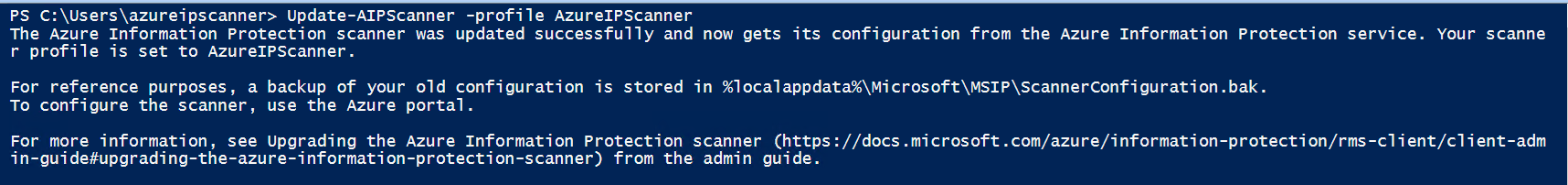
And the scanner will be connected to that profile. I expect that you can manage that connection from the portal itself soon-enough 🙂