In my previous blog I showed the current locations used by AzureIP for storing log files and event logs. I ended that article with the remark that a more central location would be preferable. And I think this will coming soon.
But in the meantime, let’s look at another Azure option: Azure Log Analytics. I was wondering if this function could be used to monitor the events related to Azure Information Protection.
It can, and more. At the end of this article, I will show you that downgrading the classification of an AzureIP labelled document will trigger an event that is picked up by Azure Log Analytics. But first: how to?
How to
In order to use Azure Log Analytics, you will need to go to the Azure portal. Here you either search for “log analytics” or go to More services | Intelligence + Analytics | Log Analytics.
From here you will set-up a new OMS Workspace.

After a little time, you will see the confirmation that the OMS environment has been deployed. Now you can start configuring which environments and what data you would like to analyse.

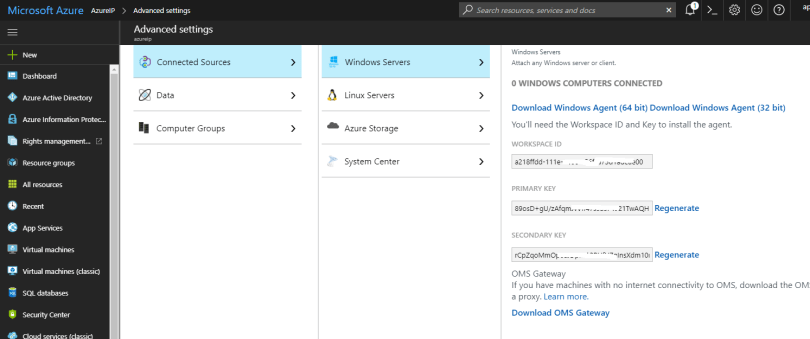
You open the workspace and go to Advanced settings. Here you can configure the sources and data. Please note two things:
- This is the location where you can find the required Windows client for your source environment(s). This is mandatory;
- This is also the location for the ID’s and key’s needed when installing this client.
The client will take care of any configuration, so you don’t have to configure anything yet. Let’s look at the data part. As I want to monitor certain events, I add a Windows Event Logs data source.
You can add any Windows Event Log. The interface provides you with a list of the most standard ones. But you can type the name of any existing event log. If you don’t know the name, then go to the event viewer. Right-click the event log and select Properties. There’s your name 🙂

This basically ends the configuration for now. Let’s look at the client.
Client
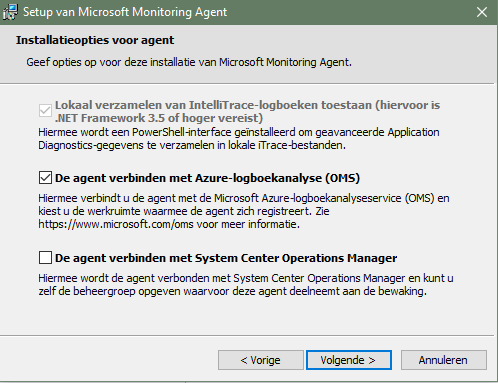
I installed the client from the download page as seen above. You will need to configure the client to connect to OMS and have the workplace ID and keys ready! Please note the connectivity. The client requires a connection to OMS and can be configured to handle proxies. See the documentation for this.

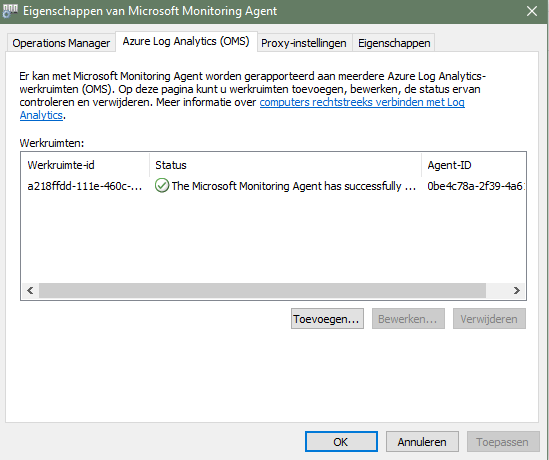
After configuration, you’ll notice little. This is to be expected, as you’ve just installed a Windows Service. You can find the client here: C:\Program Files\Microsoft Monitoring Agent\Agent (for the 64 bit client, that is).
You can start the client to check if everything is up-and-running.
Results
Please allow the client so time to send the information to Azure Log Analytics and save some time as-well for Log Analytics to process the information. In the end, you can start looking at events. You go to Log Analytics | Log search and here you’ll find a query based interface.
To get an overview of all events, you can use:
Event | summarize AggregatedValue = count() by EventLog
The results can be exported or used in PowerBI.
But you can also select a specific event log, if you have more than one. For example, Azure Information Protection:

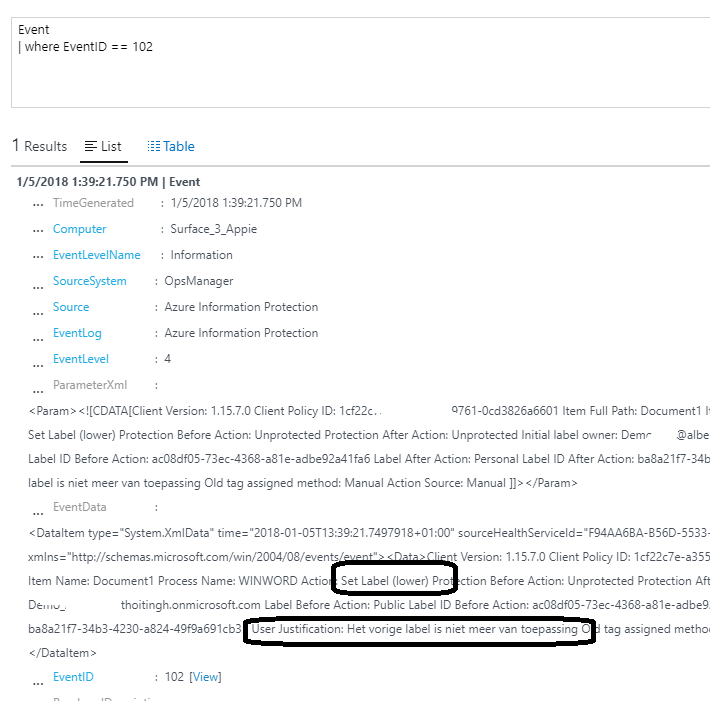
Or, just use the relevant eventID. When the AzureIP classification of content is downgraded by the user, this triggers an eventID 102. So you can use this query:
Event | where EventID == 102
As a test, I downgraded a Word document. And this event was found by Azure Log Analytics.
Concluding
In this article I wanted to show you that you can aggregate AzureIP event log entries to a central level. I have not tested this in an enterprise wide environment or looked at ways to automate this process. But I do hope this gives some information.
More information can be found at Microsoft: https://docs.microsoft.com/en-us/azure/log-analytics/
Thank you very much for the information.
Hi Albert,
In order to collect “azure Information Protection” event logs from client into Log Analytics, do we need additional solutions on Log Analytics?
I do a test on a Azure console, create a new workspace with only Log search solution (without security or others solution). I try to add the name of the event log in advanced setting, but I cannot find Azure Information Protection.
Appreciate your advise. Thanks.
Hi there,
Sorry about this. You can just add “Azure Information Protection” as the name for the event.
This should work.
Kind regards,
Albert