One thing we must realize when using Azure Information Protection (AzureIP) is that any (event)logging will be stored on the local machine. And this is a little drawback.
Let’s say I have one or more users who are in the habit of downgrading the classification of content. This can be solved by using mandatory classifications, but this isn’t always possible or recommended to do.
So in this case, I might want to know when these downgrades occur and by whom. Unfortunately, AzureIP does not provide us with an overview of these events. During Ignite (last september 2017) this kind of functionality was announced and I expect it to become part of the AzureIP dashboard and Office 365 security & compliance center.
In the meantime, here are some locations you might want to look at when using the AzureIP client.
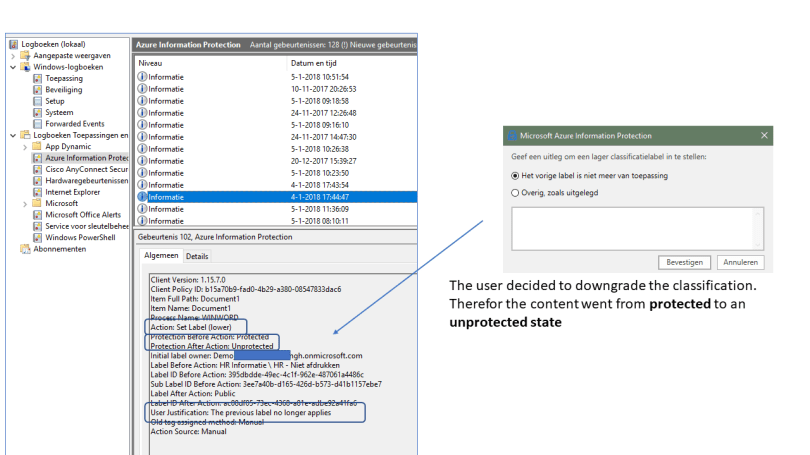
Eventlog
In the Windows Eventlog all Azure Information Protection events can be found. Including the downgrading of the classification. This can be seen below.
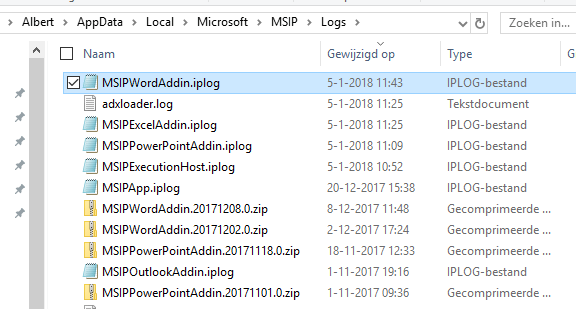
Logs and configuration
Other logs and configuration are found in the AppData\Local\Microsoft\MSIP folder. Here you can find the logfiles (.log) and policy files (.iplog).
The .iplog files contain all information of the policies used by the AzureIP client. When your reset this client, these files are deleted and re-downloaded from Azure. Here’s an example of such a file.
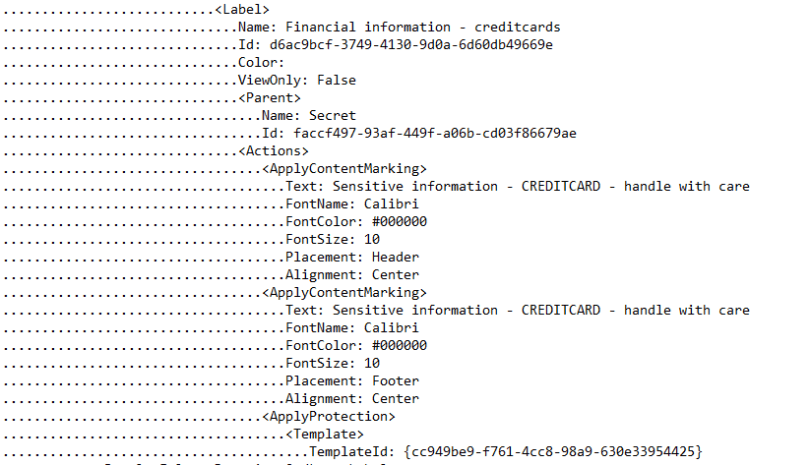
You will notice that this information is about the label “Financial information – creditcards”. It has visible markings and when used, it will protect the content (see the TemplateID).
The other type of file (.log) is precisely that: a log file. Here’s an example.
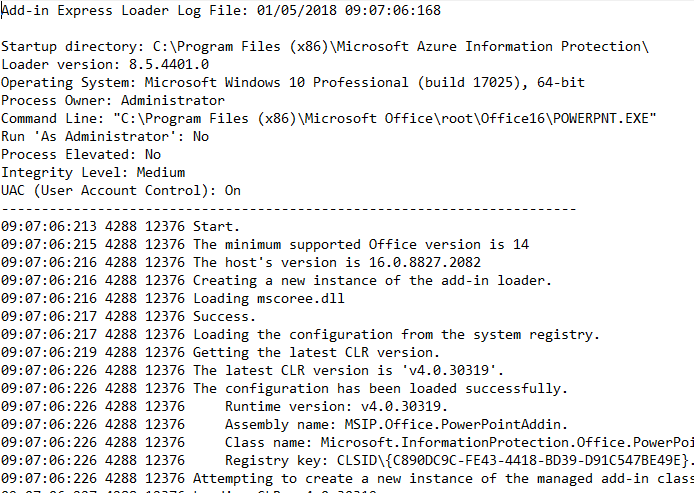
As you will notice, every Office application has it’s own log file. The example above is for PowerPoint.
So….
Again, these files and other information can be found on the local machines and will help you when you need to troubleshoot. However, a more central way of monitoring these logs would be nice.
And there is: Azure Log Analytics. Read all about that, here….
More information can be found here:
One comment