In most of my blogs I describe the functionality or technical functions related to information protection. And this is fine – for theory. But what about the practical side of things? What if you want to start using Azure Information Protection with real-life people?
At one of our clients we’re piloting this new functionality. Based on some initial demonstrations and awareness sessions, the consensus was:
- This is great!
- Why don’t we have this already?
So, a good basis to start a pilot. And finding people willing to participate in a pilot was not difficult at-all. But then the fun really starts and multiple questions need to be answered. Let’s take a look at some of them.
Do you know the scope of the pilot?
What are your going to pilot in the first place? Just classification or protection as-well? Do you need to have the e-mail protection added as-well or just the integration with Office or the Explorer? These are some of the issues you will have to face.
You will also need to set a time frame for the pilot and determine what happens after the pilot. Will you de-install all clients and have encrypted documents decrypted by the super-user (hint: have a super-user role defined)?
Are all technical requirements met?
You will need to know how the Azure Information Protection client will be installed. Also check if all pilot participants have the required license to participate in the pilot. Check out the technical requirements for Azure Information Protection. And test the functionality yourself to make sure that everything is OK.
Do you know your pilot group?
You will need to know the pilot participants and if this is just one department/team or people working throughout the company. In our case: the latter. We also need to know how these people work and if this pilot will not interfere in their day-to-day processes.
Do you know your environment?
You should determine if you are going to do the pilot in a dedicated pilot environment or using the production environment. The latter is more easy, but will also offer some challenges. For example: can you provide the users with the required client and will they be able to sign-in? But more importantly: if these people are going to protect content (encryption), is there a risk that people outside of the pilot will not be able to use the content?
All these questions need to be answered. In our case, we were using the production environment. People were using their own workstations and login credentials. We made provisions for the non-pilot users.
What labels to use?
One of the best-practices by Microsoft is to use “recognizable” labels. And this makes great sense. When using labels like “confidential” or “internal” you will have to challenges:
- People won’t know what is confidential or highly confidential (for example);
- If “internal” is used to label all content which is not to be protected (as it’s also shared with your external partners), then the name doesn’t make sense. So, choose Public instead 🙂
So, choose wisely on this. The “problem” is that most companies use the standaard CIA levels for classification. And these are mostly Internal, Confidential, Highly Confidential, Secret.
In our case, we ended up with a scheme of Public, Confidential and Strictly Confidential. Not my first choice, which was more like this:
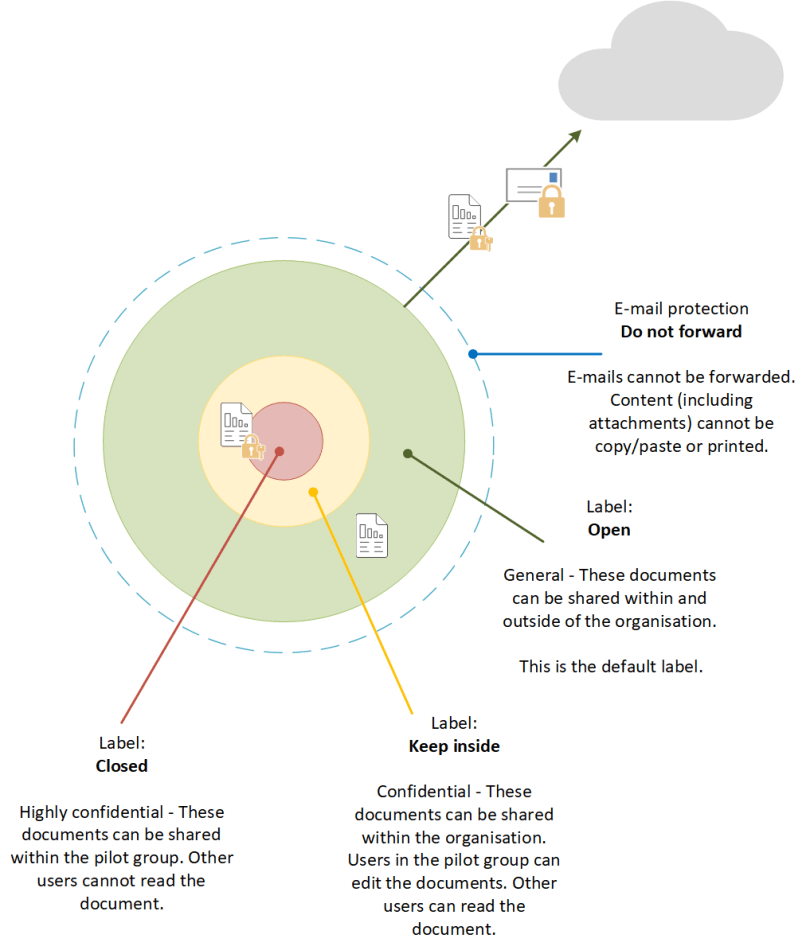
What should these labels do?
Together with the business you should decide what actions are related to the labels. For example: does the label offer any visual markings and should labeled content be offline available? Will you provide any protection to the content, based on the label? If so:
- What level of permissions?
- How do these permissions apply to (tip: use groups);
- Will you use the Azure key management or will you “bring your own key”.
Please do take into account any users which will not be participating in the pilot. You need to determine if these users will need to have access to the content. If so, you need to include them into the permissions.
What to tell everyone?
When starting the pilot, you will need to explain a lot of stuff to a lot of people. Don’t underestimate this. The more information, the better. A lot of people will be wondering what the pilot is about, what it will do, what problems will arise from the pilot, and so on. So be prepared for this!
You need to tell the pilot users and non-pilot users on what to expect. Explain in great detail what the labels represent and what actions (see above) are related to these labels. If you intend to use the e-mail protection, be sure to explain the Do not forward (or any other e-mail encryption) action as it relates to labels. For example: if you protect a document and send it using e-mail, the e-mail itself is not protected…..
In our case, we took the time to inform them using a kick-off session. And during the pilot, we talked weekly to some key-users on their experiences so-far.
You will also need to inform your IT people. Ranging from the servicedesk, service delivery management, workplace management and your security officers. Tell them what you are going to do and make the necessary arrangements for any changes. You don’t want your pilot to be put on hold, because someone was not “in the loop”.
How to tell anyone?
Have a lot of information ready. Microsoft provides lots of fact sheets, example e-mails, you name it. But you will need to re brand this to your situation. In our case, we had a lot of supporting material, including a list of PtbAQ (Probably to be Asked Questions). Try to think of any situation or question which might pop-up and answer it already 🙂
What about after the pilot?
Plan ahead. You need to know what to do with the evaluation of the pilot. Perhaps you’re going to need additional pilots with added functionality. Or maybe you want to move towards a production release. Determine this before the pilot starts. Plan ahead.
All in all
Based on my experiences thus-far, I would recommend these steps when preparing to use Azure Information Protection. This is my take on this. Please refer to the Microsoft site for more info.