Conditional access to any Office 365 functions is highly recommended. It enables many controls like multi-factor authentication, location-based access and even dynamic access based on certain risks.

Multi-factor authentication (MFa)
MFa is an additional security feature. It requires the user to enter a second factor, after he/she has provided a valid userid/password. This second factor can be a text-message on the user’s phone, an e-mail or using an authentication app.
Some applications do not support MFa. In order to still become very secure, you can use a so-called app password. This password is added to the application, so you can access the environment. Even Office 2010 (see below) can use these app passwords, but only from version 14.0.7182.5000.

Theory vs. practise
MFa is great and can easily be configured in the Office 365 security& compliance center. But do be careful with this, as it might not work exactly the way you planned…. And the reason why can be found in the except of this Microsoft article.
You can use Azure AD conditional access to protect cloud apps when an authentication attempt comes from:
- A web browser
- A client app that uses modern authentication
- Exchange ActiveSync
Some cloud apps also support legacy authentication protocols. This applies, for example, to SharePoint Online and Exchange Online. When a client app can use a legacy authentication protocol to access a cloud app, Azure AD cannot enforce a conditional access policy on this access attempt. To prevent a client app from bypassing the enforcement of policies, you should check whether it is possible to only enable modern authentication on the affected cloud apps.
Examples for client apps conditional access does not apply to are:
- Office 2010 and earlier
- Office 2013 when modern authentication is not enabled
See the text in bold? That might become a problem. Let me explain.
Classic authentication
As we all know, there are still a lot of organisations that use out-of-date technology. I’ve seen SharePoint 2003/2007 environments stills going strong or even Office 2010 implementations.
And Office 2010 is more than 8 years old! Perhaps even more than 10 years, as Microsoft started work on that application long before it was launched. Updates and service packs notwithstanding, these platforms can cause problems. And in this article I’ll briefly discuss a problem with MFa.
Case
Let’s take the case where an organisation, in order to support these legacy clients, needs to set Exchange Online and SharePoint Online to allow classic and modern authentication.
In order to provide a safe environment, the organisation also implements conditional access. Any connection to the Office 365 environment from outside of the corporate network is protected using MFa. And this works like a charm when using the web-browser.

Unfortunately, additional controls have not (yet) been enforced. For example, limiting which kind of clients can connect from different locations. Also, the Office 2010 environment was not provisioned with app-passwords. So both classic and modern authentication was supported.

So, what’s the problem?
The problem is very, very simple and dangerous. Because MFa does not work with clients that do not support modern authentication, this additional challenge is not presented to the user. A simple user-id/password is enough to access a mailbox.
And these clients are not just outdated Microsoft Office applications. I’ve tested this with a brand-new version of Mozilla Thunderbird. And even with MFa enabled, I could access my mailbox.
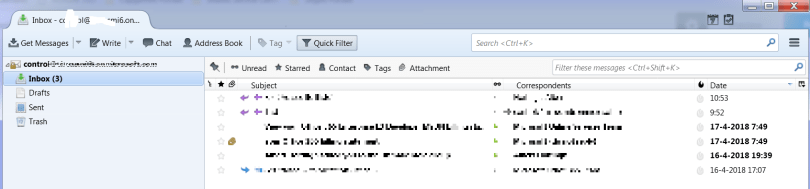
This screenshot doesn’t say very much, but you’ll have to take my word for this….. Accessing a MFa protected mailbox, without an app password, with just a userid/password.
Again: so-what?
What I’m trying to say is this; Don’t assume that your environment is save because you’ve implemented MFa. Look further then this. A simple loss of userid/password by a user can result in a breech. Conditional access policies have more options to create a secure environment. Use them!
And while your busy, try to move away from those legacy environments as-well. And read the documentation by Microsoft. Because these kinds of scenario’s can be avoided.
More information
This article describes how you can enabled/disable Exchange Online to modern authentication. You cannot force modern authentication (in my opinion). This article describes Office 365, MFa and modern authentication.