Approx. reading time: 3,5 minutes
Sensitivity labels have come a long way. First introduced as a way to get Azure Information Protection labels integrated with Microsoft/Office 365, they are now integrated into Office ProPlus and Office Online (preview), making it really easy to work with.
During Ignite 2019 a new function was announced. New? Well, sort-off. It was part of a preview program a long time ago – disappeared – and now it’s back 🙂 This function? The ability to apply sensitivity labels to “containers of information”, or in other words: Microsoft Teams sites, Microsoft 365 groups, and SharePoint sites.
What do these labels provide?
In addition to all other functions, you can now use the sensitivity labels to modify these settings:
- Public/private;
- External users access;
- Access from unmanaged devices.
Please note, and I cannot stress this enough, that the content in the “container” (site/Team) will not inherit the label that has been placed on the container. Microsoft is working with a preview for auto-labeling content in containers.
Conditional access
For this blog I want to look at the conditional access option – access from unmanaged devices. Using a label you can now control what access is provided to users with an unmanaged device. Is this new? Nope. Site-collection based conditional access has been around for a couple years. But from an admin and governance perspective it’s great to be able to use a simple label.
But it’s more then just configuring the labels. It is relevant to set-up an Azure AD Conditional Access policy as-well. Before I show you how, I just want to share a simple, but effective, PowerShell cmdlet.
The conditional access settings for SharePoint Online can be set on a tenant level (https://tenant–admin.sharepoint.com/_layouts/15/online/AdminHome.aspx#/accessControl). But we’re talking about conditional access on site-collection basis. And you can using this cmdlet to check the status:
Get-SPOSite -Identity https://<site-URL> | ft ConditionalAccessPolicy
I’ve included the result of that cmdlet in the screenshots below. So, let’s take a look.
Limited access
For Teams and sites which require limited access (web-only, printing not allowed), I’ve configured the “Teams confidential” label. See below.
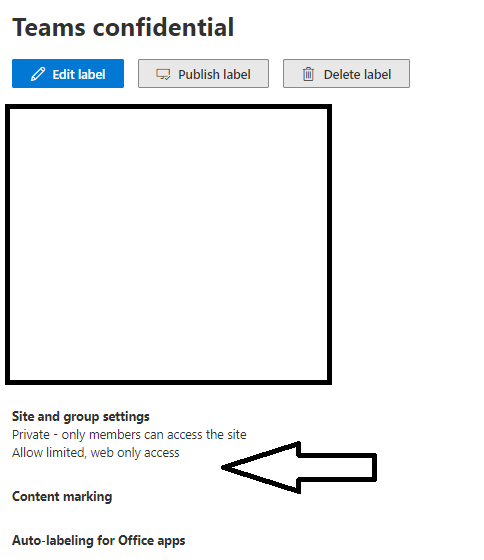
The label was created and published using a policy. In a SharePoint site (connected to a Teams site) I added the label.
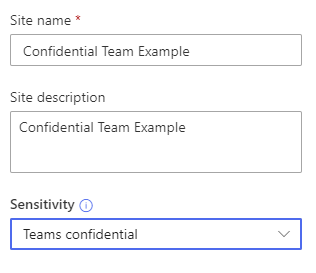
Let’s see what this does. Tip: because of tokens (etc.) you might want to use a new in-private session for this. Going to Teams and opening a (new) Word document immediately shows the conditional access in action.
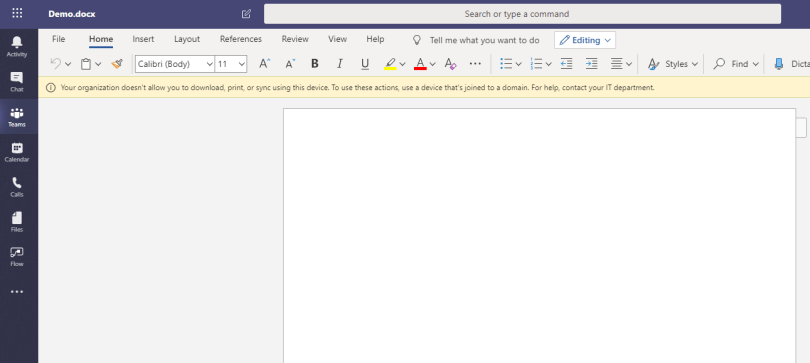
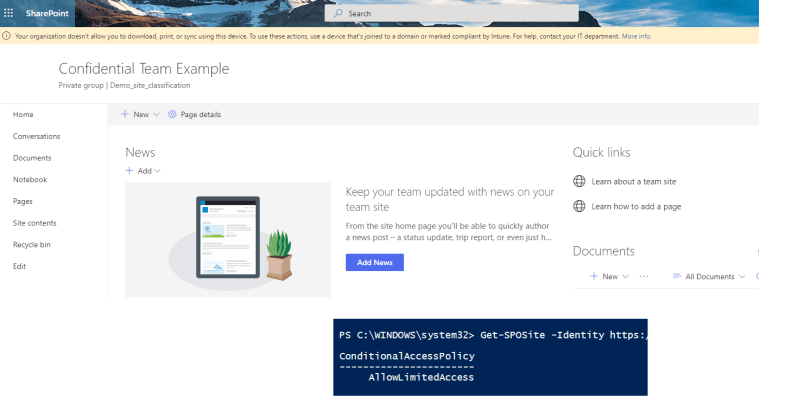
Opening the SharePoint site itself provides us with the same message. And notice the PowerShell cmdlet – the setting has been set correctly.
Blocked access
Now that limited access works, let’s go one level further. Block the access.
So I’ve created a label to configure just that.
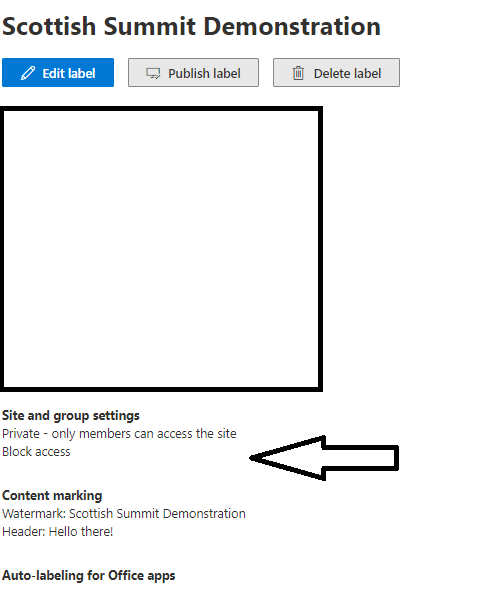
It’s a label I used for my session in Scotland 🙂
I’ve added this label to my Teams and SharePoint site. Please note – doing this from an unmanaged device will block your access 🙂 But don’t worry, you can set another label using the SharePoint admin-dashboard….
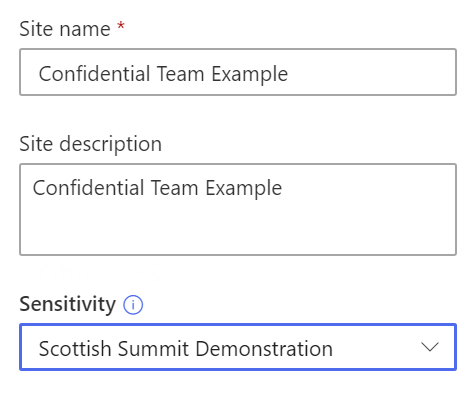
Let’s see how this works from Teams. First of all, Teams itself will continue to work. But let’s go to the files section.
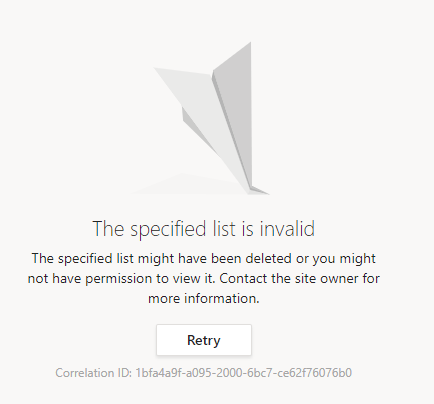
Wow. That’s heavy. This is something to communicate to your (internal and external) users. Let’s try to open the SharePoint site itself.
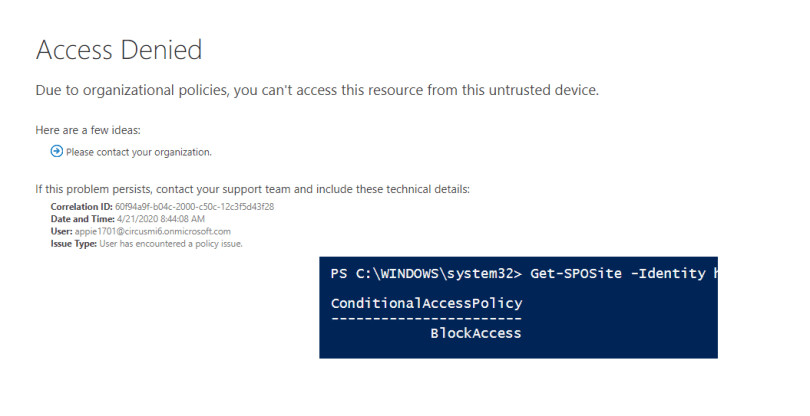
Again, notice the PowerShell cmdlet – the setting has been set correctly.
Azure AD Conditional Access
As you can see from the screens above, these labels do work. But these will require one more setting. And that’s the one in Azure AD. You will need to have a conditional access policy for these labels.
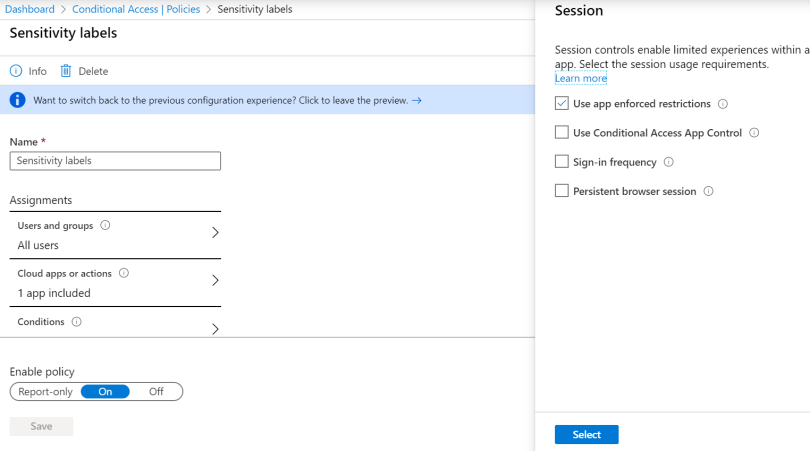
In the most basic form (as I used in this blog) this can be set to: All users | SharePoint Online | Session: Use app enforced restrictions. This will allow Azure AD to check if the app (SharePoint Online) has settings defined for conditional access. And these are managed using the labels. So….. set-up at least one of these policies in order to get the labels to work 🙂
More information
This can be found here: Microsoft Docs
But I also want to remind you of this great post on securing SharePoint: Policy recommendations for securing SharePoint
Thanks for covering this topic. We are bring out more in this area.