During Microsoft Ignite last month, one of the most innovative features presented was the new Office 365 Message Encryption or OME. This feature allows you to send an encrypted message (including the attachments) outside of your organisation.
This was already possible of course. But OME now allows Gmail, Yahoo and Microsoft (personal) users to access these messages using their own credentials!
To this end, Microsoft has set-up some form of federation between Azure Active Directory and Yahoo, Google and Microsoft itself. So basically, you can now send an encrypted e-mail to a Gmail account.
Let’s see how this works.
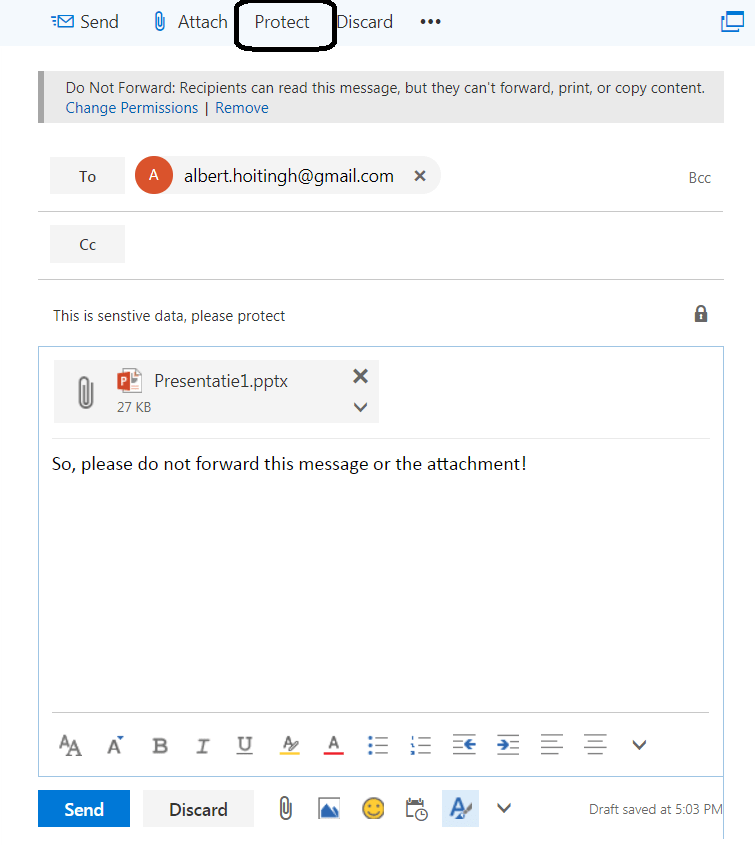
In this example I’m sending an encrypted message with an attachment to my Gmail account. First thing you will notice is the easy “Protect” button. This allows for one simple action: Do not forward.
If you want more options, that’s possible. Just select the Change Permissions option and it will show you other Azure Information Protection options. But if your content with this one, read below how to enable it.
In Gmail I receive a notification (not the mail!) that an encrypted message has been send to me. Including the typo I just noticed…..
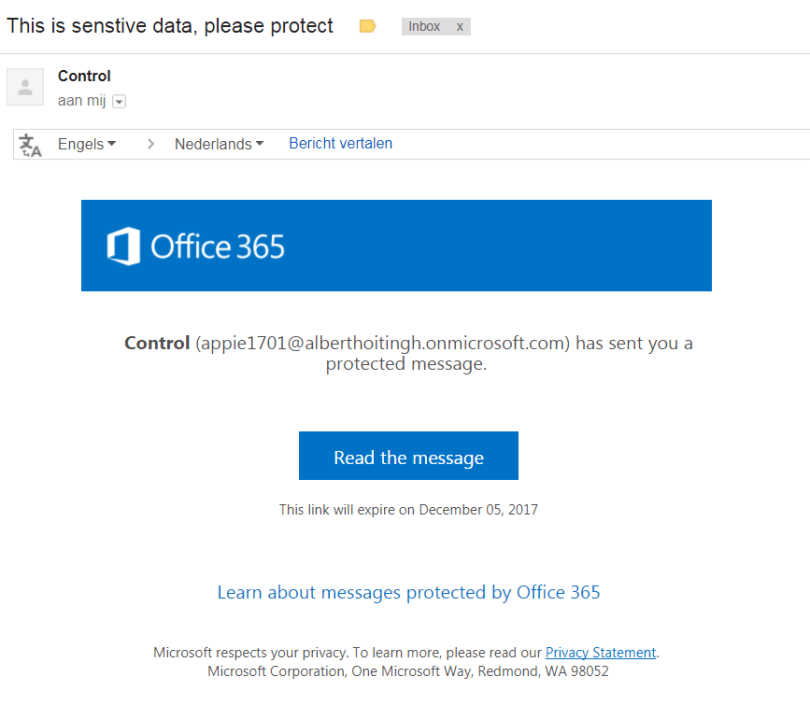
When I choose to read the message, I will be prompted to either login using my Gmail account or use a one-time pass code. It won’t make sense to forward the message to another account, because that account will not be able to open it.
By the way. Please note that the conversation is stored at Microsoft’s. Note the URL: outlook.office365.com/Encryption.
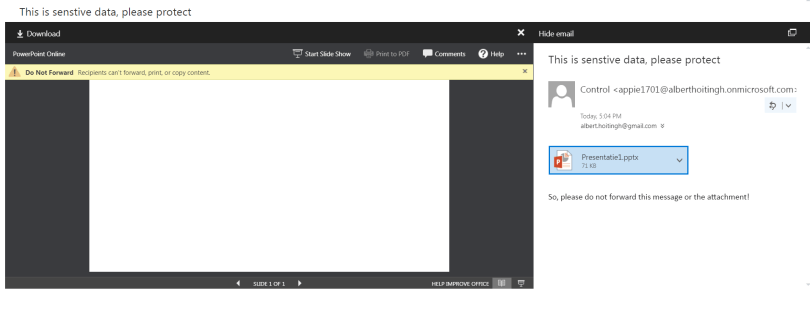
I choose to use my Gmail account and with that I’m able to access the message and the attachment. And what’s super cool: this attachment is protected as well. Note the message at the top.
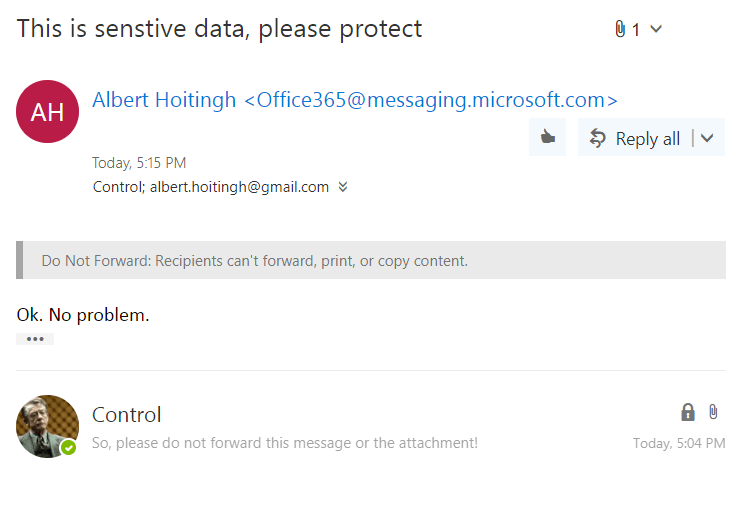
I can reply to the e-mail (but not forward or print it, of course). And it’s delivered at Office 365, where I can open the message.
As this scenario works using the web, I don’t have to install separate clients. It works on your mobile phone as easy on a tablet or workstation.
How to do this?
To enable this feature, you will need either of these two options:
- An Office 365 subscription that includes Azure Rights Management as well as Exchange Online or Exchange Online Protection (EOP).
-
An Azure Information Protection subscription and an Office 365 subscription that includes Exchange Online or Exchange Online Protection (EOP).
When you have one of these two options, you can enable OME using PowerShell.
Here’s the cmdlets to do this.
#Connect to the Azure Rights Management service.
$cred = Get-Credential
Get-Command -Module aadrm
Connect-AadrmService -Credential $cred
#Activate the service.
Enable-Aadrm
#Get the configuration information needed for message protection.
$rmsConfig = Get-AadrmConfiguration
$licenseUri = $rmsConfig.LicensingIntranetDistributionPointUrl
#Disconnect from the service.
Disconnect-AadrmService
#Create a remote PowerShell session and connect to Exchange Online.
$session = New-PSSession -ConfigurationName Microsoft.Exchange
-ConnectionUri https://outlook.office365.com/powershell-liveid/
-Credential $cred -Authentication Basic -AllowRedirection
Import-PSSession $session
#Collect IRM configuration for Office 365.
$irmConfig = Get-IRMConfiguration
$list = $irmConfig.LicensingLocation
if (!$list) { $list = @() }
if (!$list.Contains($licenseUri)) { $list += $licenseUri }
#Enable message protection for Office 365.
Set-IRMConfiguration -LicensingLocation $list
Set-IRMConfiguration -AzureRMSLicensingEnabled $true
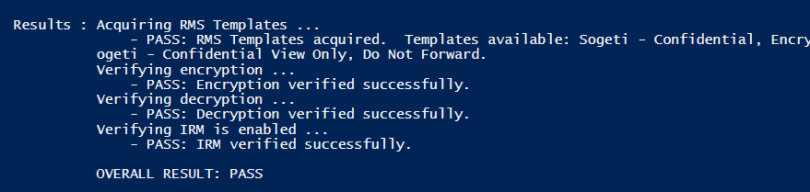
When done, you can test the configuration with this cmdlet:
Test-IRMConfiguration
Which should provide you with this output.
Which leaves only on other cmdlet. And that one sets the “Protect” button in your emails. That is done with this one:
Set-IRMConfiguration -SimplifiedClientAccessEnabled $true
And then you are all set. Easy and powerful.
I like it a lot. More information on these new functions can be found here:
2 comments